How to Stop Spam, Viruses, and Hackers Dead in Their Tracks
By Greg Reynolds
Spam Virus Help.com
Net Sense.Info
Introduction
About The Author : Greg Reynolds is a 23-year veteran of the computer industry and the President of Net Sense, an IT consulting firm. He has worked on systems integration projects with some of the largest companies in the U.S. including IBM, Bank of America, Wachovia, and Bell South.
A graduate of the University of Michigan, Greg has been hands on with computers since the days when keypunch cards were used for data entry. When he can get away with it, he likes to work on his notebook computer out on the back deck overlooking the lake.
His consulting practice with Net Sense focuses on network security and project management for corporate clients. The Spam Virus Help web site is geared toward assisting home computer users.
Greg lives outside Raleigh, North Carolina with his wife and six kids. When the five boys aren’t beating him up in various sporting activities, he serves as the First Bank of Dad for all their financial needs. And, of course, his daughter already has the keys to the vault!
About This Book: “Winning the Online Battle: How to stop spam, viruses and hackers dead in their tracks” is work in progress.
This ebook version is free for anyone to download. You have full usage and distribution rights.
You do not have the right to reprint, alter, or convert the content of this book into any other form.
Copyright Notice: This book is copyrighted, March 2004, under the laws of the United States. All rights reserved.
Version: This edition is Version 1.3. Check the web site for updates or subscribe to the Net Sense newsletter.
Table of Contents
Winning the Online Battle:............................................................ 1
How to Stop Spam, Viruses, and Hackers Dead in Their Tracks ......... 1
By Greg Reynolds Spam Virus Help.com.................................. 1
Net Sense.Info.................................................................... 1
Table of Contents ..................................................................... 3
Introduction............................................................................. 7
Building Your Castle Walls.......................................................... 9
Start with a strong foundation................................................. 9
Use the right building materials ..............................................10
Hardware firewall ............................................................11
Software firewall .............................................................12
Protect your castle from spam and viruses...............................12
How break-ins occur .............................................................13
Let right in .....................................................................13
Hand-delivered ...............................................................14
Piggyback programs ........................................................15
Guessed right .................................................................15
Summary.............................................................................16
Hiring The Right Gatekeeper(s) .................................................17
Trustworthy....................................................................17
Multi-talented .................................................................17
Multi-tasking ..................................................................18
Always on duty ...............................................................18
Updated regularly............................................................18
Gates To Guard ....................................................................18
Internet connection point .................................................19
Email.............................................................................19
Attachments...................................................................19
Backdoors ......................................................................20
Gatekeeping functions...........................................................20
Selection criteria...................................................................21
Cost ..............................................................................21
Ease of setup..................................................................22
Functionality...................................................................22
Automation ....................................................................23
Upgradeability ................................................................23
Compatibility ..................................................................23
Beware the Universal Solution ................................................24
Summary.............................................................................24
Eliminating Spies.....................................................................25
Adware ..........................................................................25
Spyware.........................................................................26
Malware .........................................................................27
Summary.............................................................................28
Acquiring the Cloak of Invisibility...............................................29
Cookies..........................................................................29
IP Tracking.....................................................................30
Email Address Theft.........................................................31
Online Communication Eavesdropping................................32
Summary.............................................................................33
Use A Multi-layered Defense .....................................................34
Best Practices - Computer Security .........................................34
Best Practices – Firewall ........................................................34
Best Practices - Spam Prevention............................................35
Best Practices – Antivirus Protection........................................35
Best Practices – Spyware/Adware Detection.............................35
Best Practices - Malware Defense............................................35
Summary.............................................................................36
Computer security for your Windows PC........................................37
Windows security patches......................................................37
Internet Explorer Security......................................................38
How to secure Internet Explorer .............................................39
Create a multi-layered defense...............................................40
Spam filters block 93.7% of your spam email ................................41
Good spam filter: Spam Agent................................................41
Better spam filter: Spam Inspector 4.0....................................42
Best Spam Filter: Spam Arrest ...............................................43
Free Spam Filters are great anti-spam blockers..............................46
Free Spam Filters For Home Users ..........................................46
Free Spam Filter #1: Spam Pal...............................................46
Free Spam Filter #2: Spam Weasel.........................................47
Free Spam Filter #3: Spam Buster..........................................48
Spam Prevention Tips: Anti-Spam Do's & Don'ts ............................49
Spam Prevention rules to live by:......................................49
Don't post your email address online.......................................49
Don't open spam, ever ..........................................................49
Don't buy anything from spam messages.................................50
Don't use spam "remove me" links..........................................50
Do use an anti-spam filter or spam blocker ..............................50
Antivirus software defeats the virus epidemic.................................52
Antivirus Review Criteria........................................................52
Our Good Antivirus Software Pick: ..........................................53
McAfee VirusScan (#3 overall) ...............................................53
Our Better Antivirus Software Pick:.........................................54
Panda Titanium Antivirus 2004 (#2 overall) .............................54
Our Best Antivirus Software Pick: ...........................................54
Kaspersky Anti-Virus Personal Pro (#1 overall).........................54
Norton Antivirus 2004: Free Download Info ...................................57
Norton AntiVirus software ......................................................57
Product Overview..................................................................57
Product Features...................................................................57
Product Problems..................................................................58
Product Pricing .....................................................................58
Free Download .....................................................................59
Norton Antivirus 2004 Update...........................................59
Free Antivirus Software...............................................................60
Free Antivirus Software #1: ...................................................60
AVG Anti-virus......................................................................60
Free Antivirus Software #2: ...................................................61
AntiVir Personal Edition .........................................................61
Free Antivirus Software .........................................................62
Free Anti Virus Downloads .....................................................63
Free Antivirus Download #1:..................................................63
Panda Titanium Anti-virus......................................................63
Free Antivirus Download #2:..................................................64
Kaspersky Anti-virus .............................................................64
Free Antivirus Download #3 ...................................................65
Norton Anti-Virus 2004..........................................................65
Free Virus Scan Websites ............................................................67
Trend Micro HouseCall...........................................................67
Kaspersky Virus Checker .......................................................68
Need a free virus scan?....................................................68
How to do your Free Virus Check.......................................69
BitDefender Free Online Virus Scan.........................................69
Panda ActiveScan - Free Online Scanner..................................70
Spyware removal protects your privacy.........................................71
What is Spyware?............................................................71
How you got infected with Spyware ...................................72
Why you want spyware removal........................................72
Spyware Removal Review Criteria...........................................73
Good Spyware Removal Pick: .................................................73
X-Cleaner from X-Block (#3 Overall).......................................73
Better Spyware Removal Pick:................................................74
Spy-Killer V3.0 (#2 Overall)...................................................74
Best Spyware Removal Pick: ..................................................76
PestPatrol (#1 Overall)..........................................................76
Free Spyware Removal Programs .................................................78
Adware.............................................................................78
Spyware ...........................................................................78
Free Spyware Removal #1.....................................................79
Lavasoft's AdAware...............................................................79
Where to download AdAware ...............................................80
Free Spyware Removal #2.....................................................80
Spybot Search & Destroy.......................................................80
Where to download Spybot Search & Destroy .....................82
Free Spyware Removal #3.....................................................82
PestPatrol (#1 Overall)..........................................................82
Spybot Search & Destroy nails 99% of spy bots .............................84
Spybot Home .......................................................................84
Why Spybot S&D gets rave reviews.........................................84
Where to download Spybot Search & Destroy...........................85
Where to get updates............................................................85
Where to get Spybot SD questions answered ...........................86
A Personal firewall keeps you safe online.......................................87
A personal firewall blocks, on average, three hack scans a day...87
What is a firewall? ................................................................87
How a firewall works .............................................................87
Hardware firewall..................................................................88
Software firewall...................................................................88
Free personal firewall ............................................................89
Where you can get a free firewall............................................89
Free Firewall Software.................................................................90
Personal Firewall Software #1 ................................................90
Zone Alarm (#1 overall) ........................................................90
Personal Firewall Software #2 ................................................91
Tiny Personal Firewall (#2 overall)..........................................91
Personal Firewall Software #3 ................................................92
Norton Personal Firewall 2004 (#3 overall) ..............................92
Firewall Downloads ...............................................................92
BlackICE Firewall ..................................................................93
Outpost Firewall ...................................................................93
Stay Safe in Your Castle ...........................................................95
Resource Links Save You Time & Money .....................................96
Spam Resources...................................................................96
Antivirus Resources...............................................................96
Spyware Resources...............................................................97
Firewall Resources ................................................................97
Ebook Resources ..................................................................98
Computer Resources .............................................................98
Webmaster Resources ...........................................................99
Security Resources ...............................................................99
Additional Resources .............................................................99
Introduction
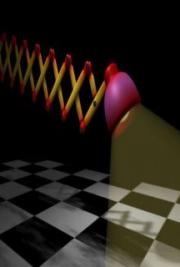
The key to winning the online battle is to think
medieval. And no, that’s not really as odd as it sounds.
You need to be a little Machiavellian – building up your castle walls, hiring the right gatekeeper, eliminating spies, and acquiring the cloak of invisibility – to win the online battle.
Then, once you have good defenses in place, you can protect easily protect yourself while you venture online as long as you keep your head about you.
And how do you do that?
Simple. You just use common sense:
· You don’t leave the front door open at your castle. · You don’t let anyone in unless they know the password. · You don’t let spies leak valuable information. · You don’t let anyone see where you’re going.
So how does that translate to staying safe online?
You put systematic procedures in place that watch your back. When you are connected to the Internet, no one can possibly keep up with all the communication process going on between your computer and the outside world.
However, by using a combination of specialized programs, you can put a multi-layered defense that monitors all the communications to and from your computer and keeps your castle safe.
Every online computer needs the following:
· Personal firewall
· Spam filtering
· Antivirus protection
· Spyware/malware detection
With these tools you can easily win the online battle and stop spam, viruses, and hackers in their tracks. The next few chapters will walk you through the basic concepts followed by chapters describing how these products work, covering best practices, and providing detailed product information.
Building Your Castle Walls
In medieval times, castle walls provided a good defense against attackers. Sure, there were still some risks such as bad guys scaling the walls, sneaking in the gates, or shooting flaming arrows over the walls. But, all in all, living behind strong walls was a lot safer than being unprotected.
The same holds true today. Your computer is your online home and it needs to be a fortress to protect you from attack.
In other words,
PC = Home = Castle.
So, how do you go about turning your computer into a fortress? You begin by building your castle walls. We’ll get to guarding the gates, becoming invisible, and knocking off pesky spies in future chapters.
Start with a strong foundation
To build strong castle walls, you first need a good foundation. With your computer, that means having your hardware and software up-todate, all the holes in your computer’s operating system plugged, and any necessary patches applied.
Otherwise, your foundation will be weak because the building blocks weren’t strong enough to handle the load. The unpatched operating system means the mortar was weak, causing holes and weak spots to be left in your castle walls.
Today ’s programs place more demands on your computer than ever before. You need a fast enough processor, sufficient memory, and a large enough disk drive to handle all the work. Otherwise, you won’t have enough men to defend your castle.
Most home computers today come with enough processing power, but are woefully short of memory. Imagine defending your castle with soldiers who couldn’t remember what they were supposed to do and had to stop and think about it before acting.
By then, things may have gotten out of control. Or, worse yet, everything will happen in slow motion as your computer slows to a crawl.
Windows computers need a ton of memory to handle the many processes they are running simultaneously. When you build your castle walls, you’ll be adding even more tasks to their to-do list.
Do your computer a favor and give it sufficient memory to do all the jobs quickly and easily.
At a minimum, Windows XP systems should have 512k of memory. By upgrading your computer’s RAM memory to that level, you’ll ensure that every task is handled swiftly.
Likewise, having enough disk space is critical to your system ’s performance. Today’s software programs are enormous compared to the programs in use a decade ago.
As you add more files to your hard drive, the response time slows as more data is searched to find what is needed. If you find your system slowing down, check and make sure that you have enough space available on your hard drive.
For more information about all the various performance settings to check and adjust on your computer, see the Chapter on “PC Settings Best Practices”.
Use the right building materials
Once a good foundation is in place, it’s necessary to use quality materials to build your castle walls. The basic building blocks are:
· Hardware firewall · Software firewall · Antivirus protection · Spam prevention
A computer firewall is simply a hardware device or software program that allows into your computer only the programs and data you decide are acceptable. Firewalls are the best defense a computer can have. Simply put, a firewall detects, rejects, and protects.
Hardware firewall
A hardware firewall is an external device that resides outside your computer. A software firewall is a program that resides inside your computer.
Both types of firewalls analyze all incoming and outgoing traffic according to preset rules. You can also add additional instructions to your firewall that will allow certain types of additional communication.
Using a hardware firewall on a home computer is rare as they are designed to isolate and protect computer networks. Taking our castle walls analogy a little bit further, these are like walls that protect an entire town or city.
In some cases though, you might use a hardware firewall at home. Many people network their home computers together and connect to the Internet through a single, high-speed connection, usually cable or DSL.
Several manufacturers include firewalls within the cable/DSL routers sold in most home electronics stores.
These hardware firewalls disguise everything behind them with their own unique addres